There's a common misconception in enterprise IT: "Our data is hosted in Canada (or France, or Germany), so we're fine." This assumption is dangerously wrong.
The Jurisdictional Reality
The US CLOUD Act, enacted in 2018, gives American law enforcement the authority to compel US-headquartered technology companies to hand over data — regardless of where that data is physically stored. If your cloud provider is Microsoft, Google, Amazon, or any US-incorporated company, your data hosted in Montreal, Paris, or Frankfurt is still reachable by US authorities.
FISA Section 702 goes further. It authorizes the surveillance of non-US persons outside the United States, using data processed by US providers. This isn't theoretical — it's operational, and it applies to enterprise data flowing through Microsoft 365, Azure, AWS, and Google Cloud.
Why This Matters Now
Three forces are converging to make this a board-level issue:
Regulatory pressure is accelerating. Quebec's Law 25, the EU's NIS 2 directive, and RGPD enforcement are all tightening requirements around data residency and jurisdictional control. Organizations that can't demonstrate control over their data's jurisdictional exposure face real compliance risk.
Government contracts are shifting. Both Quebec and France have published sovereignty doctrines in 2025-2026 that explicitly address extraterritorial risk. Government procurement is moving toward providers that can demonstrate jurisdictional independence.
The insurance and audit landscape is catching up. Cyber insurers and SOC 2 auditors are increasingly asking about jurisdictional exposure as part of their risk assessments.
The Practical Framework
We use a three-step approach with our clients:
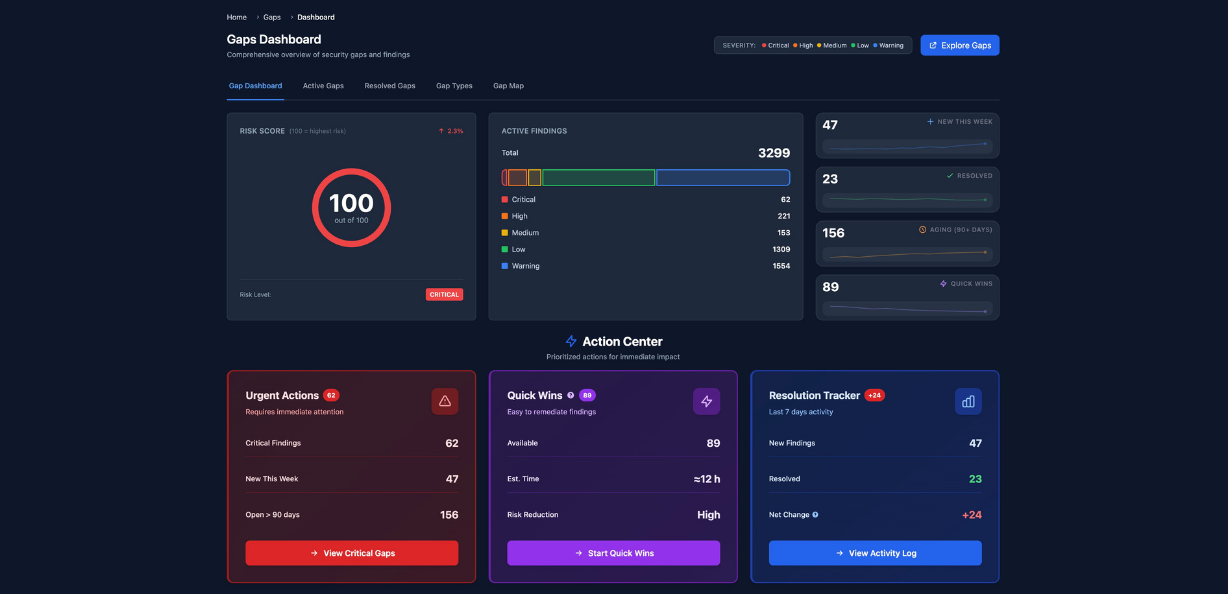
Step 1 — Map the exposure. For every system, every SaaS subscription, every cloud workload: who is the provider? Where are they incorporated? What jurisdiction governs data access? This can be done in under 14 weeks with the right methodology.
Step 2 — Classify and prioritize. Not all data carries the same jurisdictional risk. Personal health information, defense-related data, and citizen records need sovereign hosting. Internal productivity tools may not. The classification determines the migration priority.
Step 3 — Design the hybrid architecture. Keep what can stay in Azure. Move what must move to sovereign infrastructure — OVH, Infomaniak, Scaleway, or on-premise. Design the boundary, not the binary.
The Bottom Line
Jurisdictional compliance isn't about leaving Microsoft. It's about knowing exactly which workloads are exposed, which regulations apply, and designing an architecture that satisfies both operational efficiency and legal requirements.
The organizations that act now will have a competitive advantage. The ones that wait will be forced to act under pressure — and that always costs more.